Not-for-profit Programs
Alacrity Canada in Victoria, British Columbia is a partnership focused on promoting technological entrepreneurship and regional investment opportunities in Western Canada.
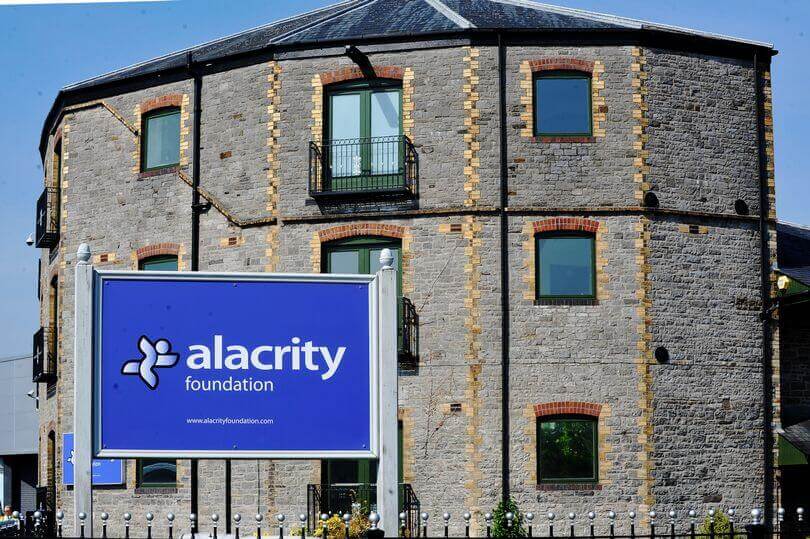
The Alacrity Foundation UK in South Wales is a unique educational charity supported through Government grants and private philanthropic donations. The Foundation mentors and trains graduate students to create a new generation of UK-based technology companies.
International Investment Funds
The Alacrity model varies based on regional requirements, but the commercial vision remains – enable young business leaders around the world to create industry-best new companies with the support of key local and international resources.
Accelerators
Part of the Alacrity ecosystem, L-Spark is the destination for Canadian technology start-up companies and the broader community to learn, share, execute, measure, adjust, scale and succeed. The L-SPARK Accelerator programs provide companies with access to leading technology and experienced mentorship to help build their business, grow revenues, raise capital and reach global markets.

